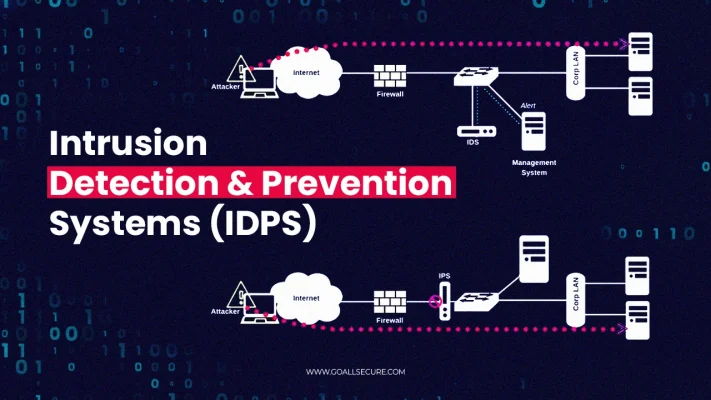
Intrusion Detection and Prevention Systems (IDPS)
Our IDPS solutions detect and mitigate threats in real time. Using OWASP guidelines and NIST SP 800-94, we deploy advanced detection tools to identify and prevent unauthorized activities within your network.
5-Step Methodology
System Deployment
Implement and configure IDPS tools.
Baseline Establishment
Define normal network behavior.
Threat Detection
Monitor traffic for anomalies.
Threat Prevention
Block malicious activity automatically.
Regular Tuning
Update signatures and settings to improve accuracy.