Web Application Firewall (WAF) Configuration
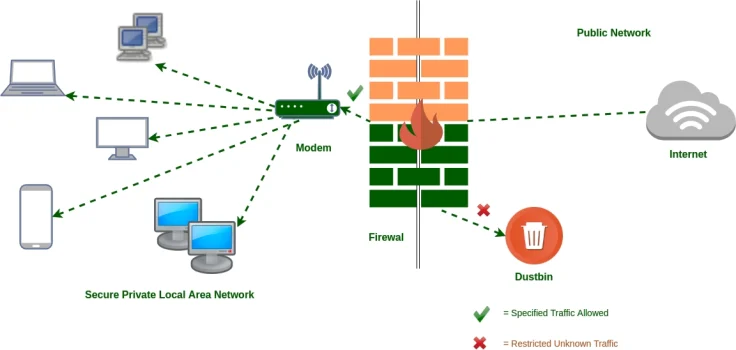
Our WAF Configuration services protect web applications from malicious traffic by following OWASP Application Security Standards. We design, deploy, and optimize WAF policies to block threats like SQL injection, cross-site scripting, and DDoS attacks while ensuring legitimate traffic is unaffected.
5-Step Methodology
Policy Creation
Develop rules based on application needs.
Traffic Monitoring
Analyze incoming requests for malicious activity.
Threat Mitigation
Block attacks using real-time responses.
Performance Tuning
Optimize WAF to reduce false positives.
Regular Updates
Adjust policies for emerging threats.