In today’s digital age, cybersecurity has become a critical component of organizational strategy. With cyber threats constantly evolving, one...
February 9, 2025
In today’s increasingly interconnected world, the integration of the Internet of Things (IoT) and Operational Technology (OT) has revolutionized...
February 9, 2025
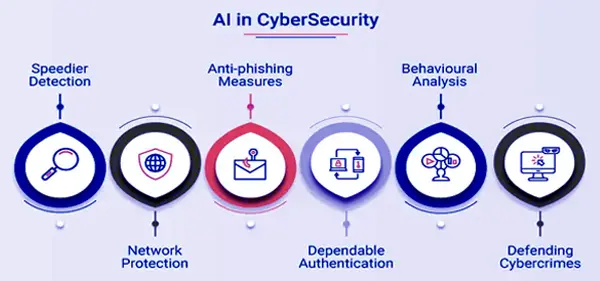
In today’s digital era, cybersecurity threats have become increasingly sophisticated and frequent. As organizations rely more on technology for...
February 9, 2025
In today’s digital era, cyber threats are becoming increasingly sophisticated, making the security of online accounts and sensitive data...
February 9, 2025
Introduction Cyber fraud has taken various shapes in recent years, with scammers leveraging fear and intimidation to extort money...
February 9, 2025
A Guide to Proactive Threat Identification and Elimination Cyber threats are becoming more sophisticated, stealthy, and persistent, making traditional...
February 9, 2025
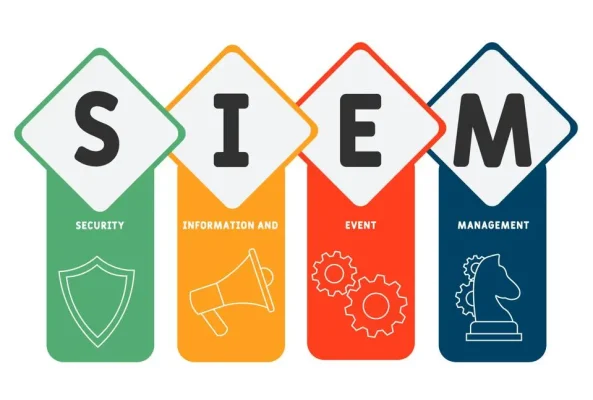
Why Real-Time Event Analysis is Critical for Proactive Defense In today’s digital landscape, cyber threats are evolving at an...
February 6, 2025
How Adayptus Consulting Helps Businesses Stay Ahead of Cyber Threats As cybersecurity professionals at Adayptus Consulting, we see firsthand...