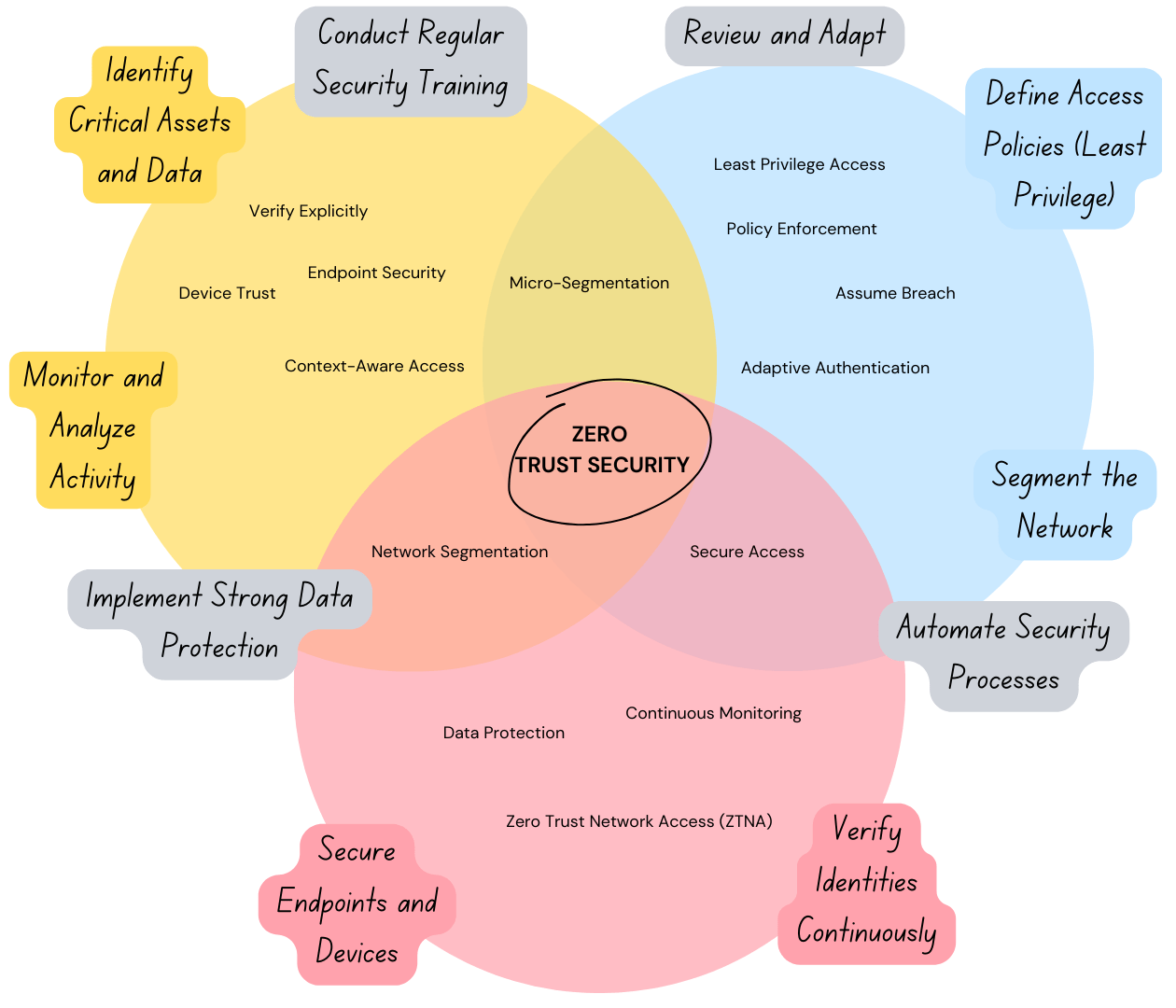
Zero Trust Security
Zero Trust Security ensures that no entity—internal or external—is trusted by default. Our solutions are designed to implement robust authentication, micro-segmentation, and least-privilege access controls across your organization. We follow NIST 800-207 Zero Trust Architecture guidelines to build frameworks that eliminate implicit trust and prevent lateral movement within your systems. This approach is enhanced with continuous user and device monitoring to detect anomalies and enforce security policies in real-time.
5-Step Methodology for Zero Trust Security
Network Segmentation
Divide networks into isolated segments to limit lateral movement.
Access Control Policies
Enforce least-privilege access based on user roles and needs.
Identity Verification
Implement multi-factor authentication and single sign-on solutions.
Real-Time Monitoring
Continuously monitor user activity and device behavior.
Policy Updates
Regularly review and update Zero Trust policies to adapt to evolving threats.