Attack Surface Management (ASM)
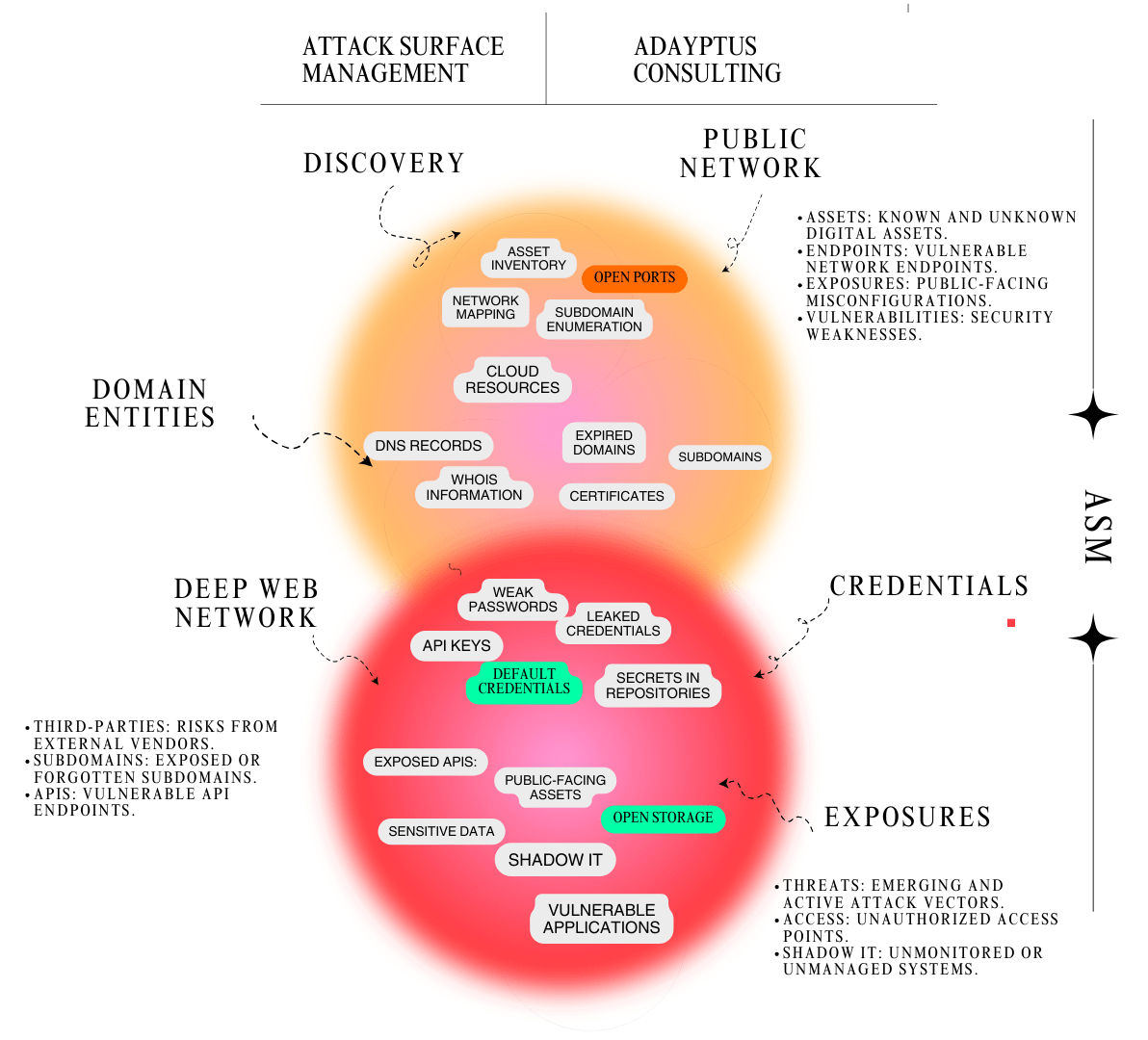
Our ASM services provide a continuous, real-time view of your digital footprint to identify exposed assets and vulnerabilities. We combine the latest scanning technologies with manual testing to map attack surfaces, prioritize risks, and reduce exposure. Following standards like OWASP Top 10, NIST Cybersecurity Framework, and ISO/IEC 27001, we ensure comprehensive coverage and actionable insights. By leveraging advanced threat intelligence, we help you stay one step ahead of attackers, protecting critical infrastructure and sensitive data.
5-Step Methodology for ASM
Discovery
Identify all digital assets, including public-facing systems, shadow IT, and third-party integrations.
Risk Analysis
Assess vulnerabilities in identified assets and prioritize based on risk impact.
Threat Simulation
Conduct simulated attacks to validate potential exploitation paths.
Remediation
Implement targeted measures to reduce exposure and harden security.
Continuous Monitoring
Maintain a dynamic view of the attack surface to detect changes and emerging risks.